China-linked APT groups target telecom companies in Southeast Asia
https://ift.tt/3jigTVs
China linked APT groups have targeted networks of at least five major telecommunications companies operating in Southeast Asia since 2017.
Cybereason researchers identified three clusters of activity associated with China-linked threat actors that carried out a series of attacks against networks of at least five major telecommunications companies located in South Asia since 2017.
“The goal of the attackers behind these intrusions was to gain and maintain continuous access to telecommunication providers and to facilitate cyber espionage by collecting sensitive information, compromising high-profile business assets such as the billing servers that contain Call Detail Record (CDR) data, as well as key network components such as the Domain Controllers, Web Servers and Microsoft Exchange servers,” states the report published by Cybereason.
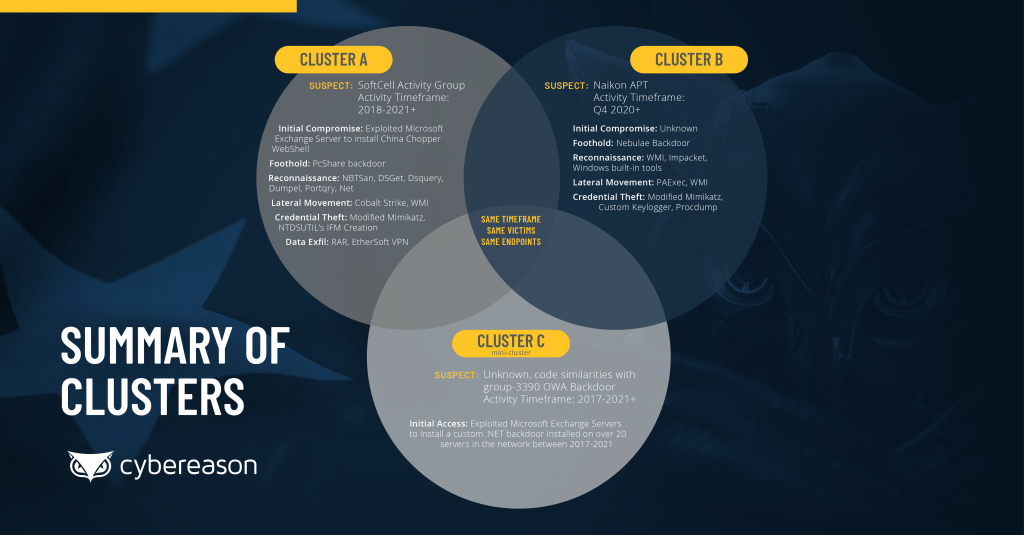
The three clusters were linked to the China-linked APT groups tracked as Soft Cell (aka Gallium), Naikon APT (aka APT30 or Lotus Panda), and TG-3390 (aka APT27 or Emissary Panda).
Below are the details of each cluster:
- Cluster A: Operated by Soft Cell, the activity associated with this cluster started in 2018 and continued through Q1 2021.
- Cluster B: Operated by the Naikon APT, the activity associated with this cluster was first observed in Q4 2020 and continued through Q1 2021.
- Cluster C: It was classified by Cybereason as a “mini-cluster” with a unique OWA backdoor that was deployed by cyberspies across multiple Microsoft Exchange and IIS servers. The analysis of the backdoor shows many similarities with a known backdoor, tracked as Iron Tiger, employed in campaigns conducted by the Group-3390 (APT27 / Emissary Panda). The activity related to this cluster was observed between 2017 and Q1 2021.

Cyber
via Security Affairs https://ift.tt/2ISWpiN
August 4, 2021 at 02:29AM